GraphQL Introspection: Exposing API Architecture
Found a production GraphQL endpoint with introspection enabled — revealing the complete API schema. How reconnaissance through introspection leads to data disclosure and exploitation vectors.
Understanding GraphQL
GraphQL is a query language for APIs developed by Facebook. Unlike REST APIs with fixed endpoints, GraphQL lets clients request exactly what they need in a single query. This flexibility is powerful — but it comes with security implications when not properly configured.
The Introspection Problem
GraphQL introspection is a feature that allows clients to query the schema itself. Useful during development, but leaving it enabled in production exposes your entire API structure to anyone who can reach the endpoint. Types, fields, arguments, queries, mutations — everything becomes visible.
Why This Matters
When introspection is enabled on a production endpoint, attackers gain several advantages:
- Complete API mapping without any guesswork or fuzzing
- Discovery of hidden fields that might contain sensitive data
- Understanding data relationships for more targeted attacks
- Identifying potential vulnerabilities through field descriptions and types
Discovery & Reconnaissance
I identified a production GraphQL endpoint at a target domain during routine reconnaissance. The endpoint was accessible without authentication, which immediately raised questions about its security posture.
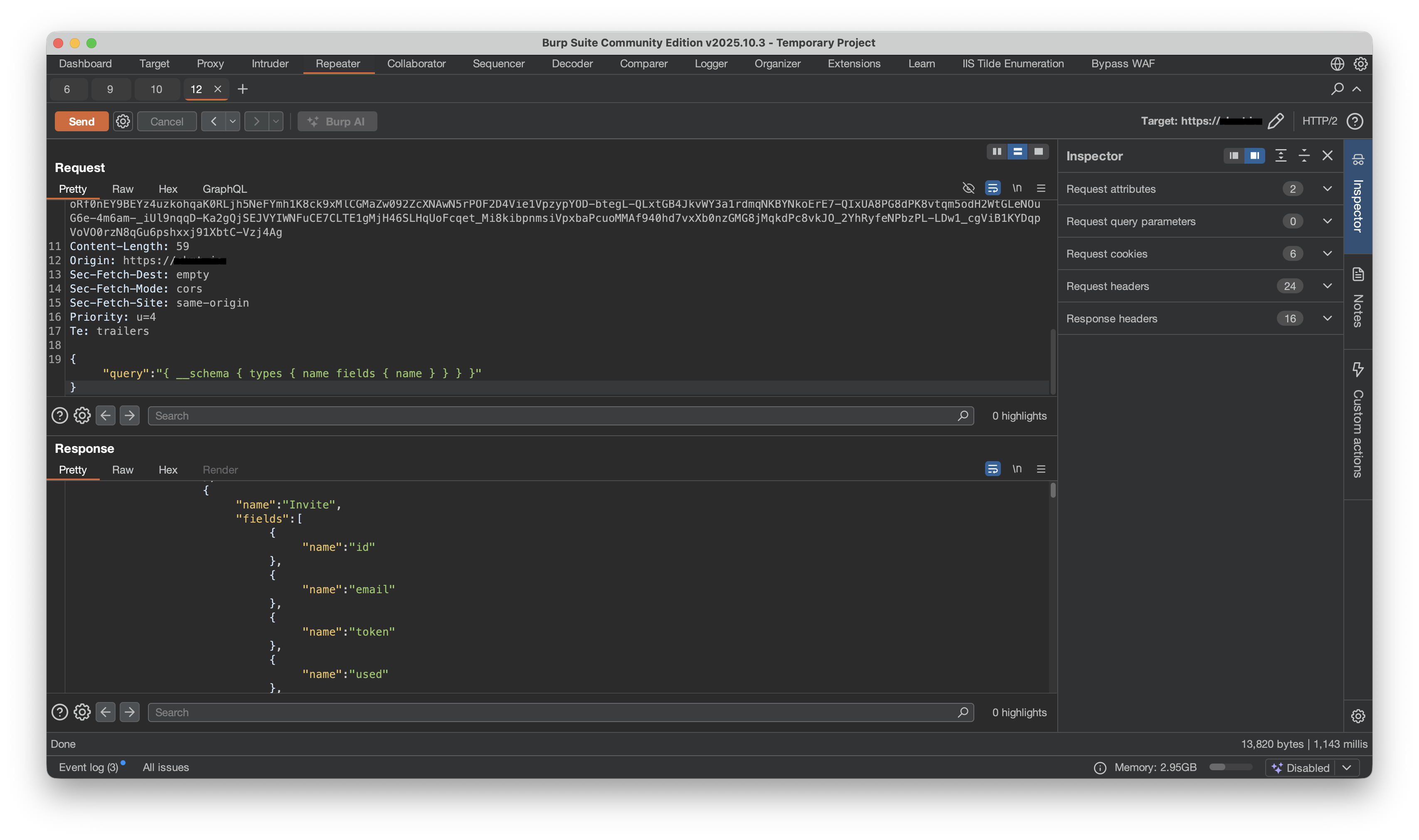
Testing for introspection is straightforward — a simple introspection query reveals whether the feature is enabled:
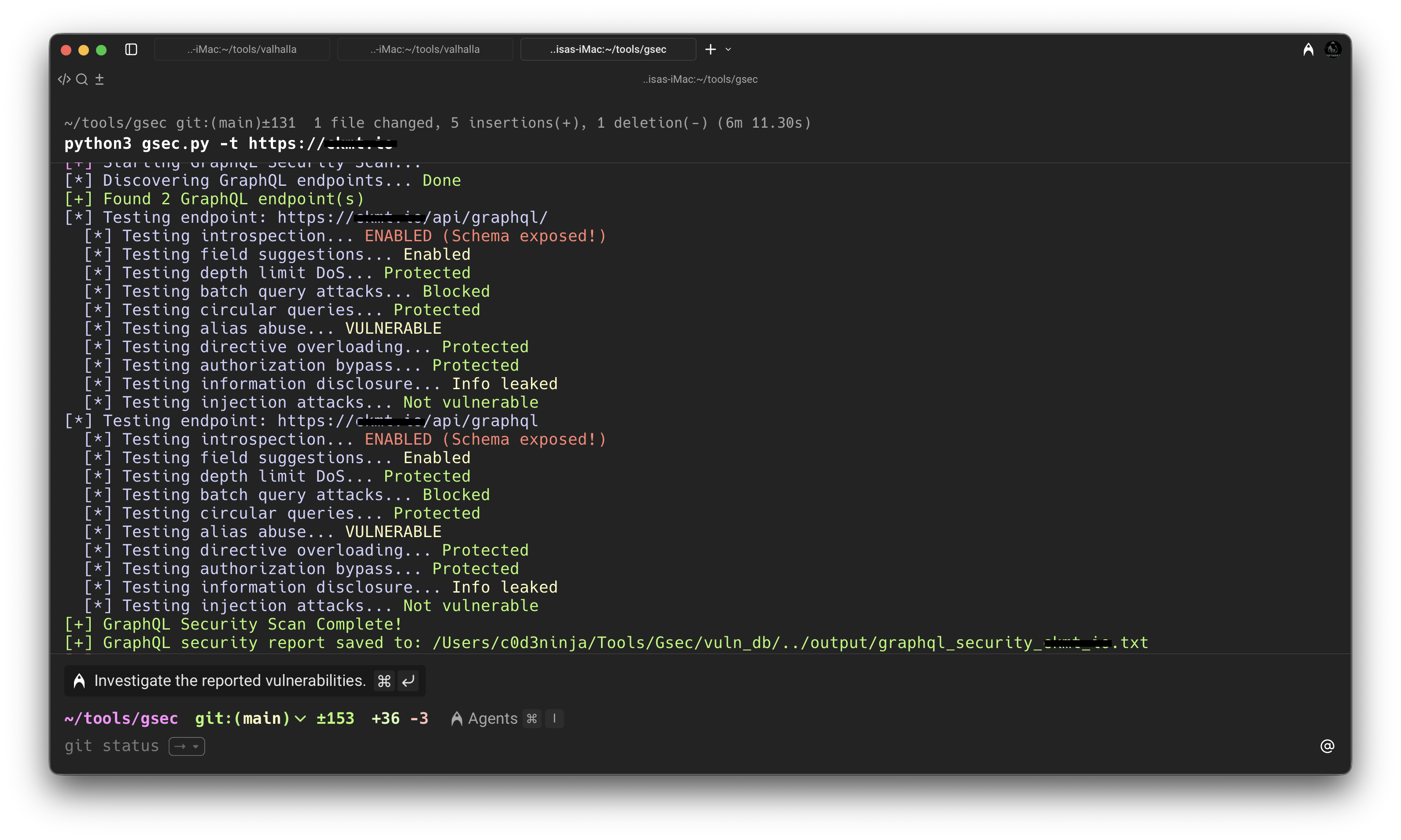
The response came back with the complete schema. Every type definition, every field, every argument — all exposed. This wasn't documentation someone forgot to take down. This was the live API structure being served to anyone who asked.
Exploitation & Impact
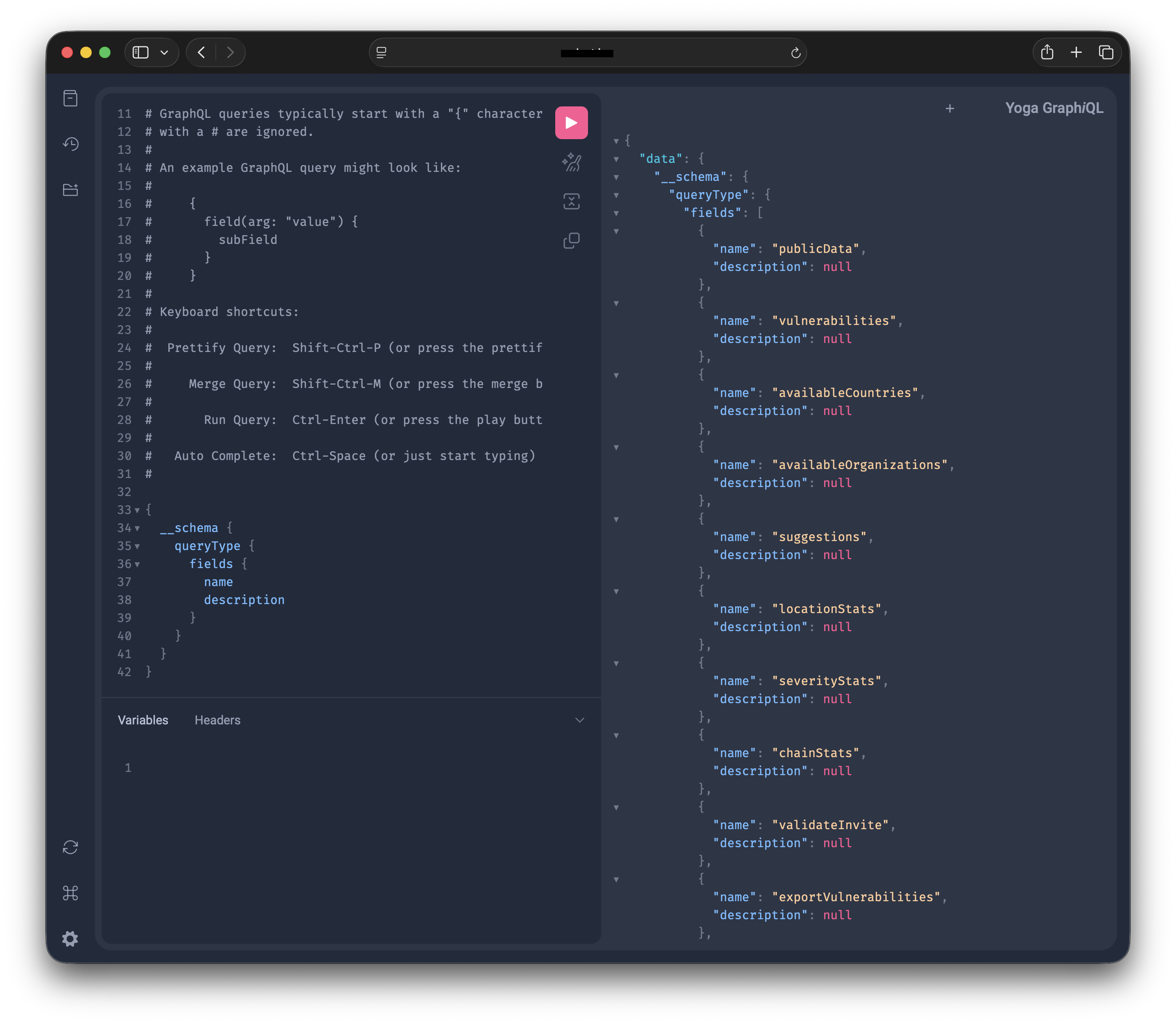
With the schema in hand, I could see fields that weren't meant for public consumption — internal identifiers, administrative flags, relationship mappings between data models. The kind of information that would normally require extensive probing to discover.
The target also had a GraphiQL endpoint enabled — an interactive playground for testing queries. What should have been a development tool was sitting in production, making exploitation even simpler.
Real-World Consequences
- Data exfiltration through carefully crafted queries targeting exposed fields
- Business logic bypass by understanding field relationships and access patterns
- Privilege escalation if admin-only fields are discoverable via schema
- Further reconnaissance to identify injection points and mutation endpoints
Mitigation
The fix is straightforward: disable introspection in production environments. GraphQL implementations typically provide configuration options to toggle this feature.
- Disable introspection in all production environments
- Remove GraphiQL and similar tools from production deployments
- Implement proper authentication before allowing any API access
- Use field-level permissions to restrict sensitive data
- Monitor for introspection attempts in production logs
GraphQL is a powerful technology, but like any tool, it requires proper security configuration. Introspection is useful during development. In production, it's an information disclosure vulnerability waiting to be exploited.